Most accounts these days require a password of some sort, and as such, the average user has countless of these codes that need to be kept both secure and top-of-mind. Some web browsers have built-in password management tools to help make them more user-friendly, but with so much convenience involved, one has to ask whether or not these built-in management tools are as secure as they should be.
NetWorthy Systems Blog
If I were to tell you that one variable was responsible for more than 80 percent of cyberattacks, what would you guess that variable was? If you guessed “stolen access credentials,” you’d be correct. The traditional username/password combination may soon be a thing of the past as more tech companies transition to alternative authentication measures.
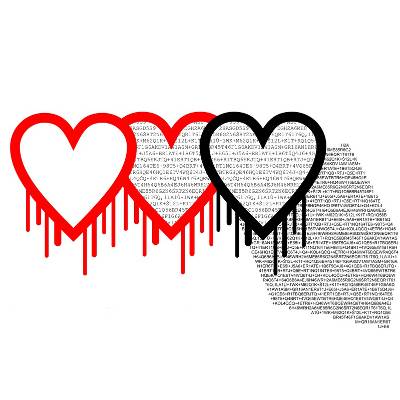 On April 7th, a new bug on the Internet was discovered that's putting millions of users' personal data at risk. Given the name "Heartbleed bug," it's capable of allowing infiltrators to collect information while you are securely browsing a SSL/TLS website. Since SSL/TLS is so widely used, it's very probably that your personal data is at risk.
On April 7th, a new bug on the Internet was discovered that's putting millions of users' personal data at risk. Given the name "Heartbleed bug," it's capable of allowing infiltrators to collect information while you are securely browsing a SSL/TLS website. Since SSL/TLS is so widely used, it's very probably that your personal data is at risk.
There is no understating the importance of strong, reliable passwords to your organization’s network security, especially to protect its wireless connection. However, this can create some friction with your staff when they try to connect to Wi-Fi using their mobile device. To make accessing the Internet easier, scannable QR codes can be used to connect to the Internet.
Security is a hot-button issue for all types of businesses, but cyber security is such a complex subject that it’s difficult to jam-pack its many intricacies into one blog article. Sometimes understanding just a few ways to improve your business’s security practices can be a significant benefit for your organization.
 Changing your password is a pain. After you’ve gone several months with the same one, it can be difficult to remember your new password. Despite this, it’s always recommended that you change your passwords often. Unfortunately, when you change all of your passwords often, it’s even easier to forget them. Instead of using a post-it note on your monitor, you should instead try using a password manager.
Changing your password is a pain. After you’ve gone several months with the same one, it can be difficult to remember your new password. Despite this, it’s always recommended that you change your passwords often. Unfortunately, when you change all of your passwords often, it’s even easier to forget them. Instead of using a post-it note on your monitor, you should instead try using a password manager.
 This holiday season might leave technology and entertainment supergiant Sony with nothing but a big lump of coal in its stocking. In a high-profile hack, hackers continue to leak Sony’s employees’ sensitive information like Social Security numbers, passports, and even personal emails. This is obviously an issue for the company, but so is its lack of IT security, as shown by their passwords being stored in a folder named “Passwords.”
This holiday season might leave technology and entertainment supergiant Sony with nothing but a big lump of coal in its stocking. In a high-profile hack, hackers continue to leak Sony’s employees’ sensitive information like Social Security numbers, passports, and even personal emails. This is obviously an issue for the company, but so is its lack of IT security, as shown by their passwords being stored in a folder named “Passwords.”
 Do you see those black clouds culminating on the horizon? They represent the possibility that hackers will gain access to your cloud storage. Though it is protected a number of ways, it will not stop an experienced hacker. To them, your defenses are as transparent as those thin, wispy, cirrus clouds that are so welcome on a boiling hot summer day.
Do you see those black clouds culminating on the horizon? They represent the possibility that hackers will gain access to your cloud storage. Though it is protected a number of ways, it will not stop an experienced hacker. To them, your defenses are as transparent as those thin, wispy, cirrus clouds that are so welcome on a boiling hot summer day.
 Last week, the Heartbleed bug was identified as a weakness in the OpenSSL cryptographic library, potentially leaking two-thirds of the Internet's secure information from any websites utilizing this encryption style. While most major websites such as Google, Yahoo, and Facebook released patches quickly, it does little to actually remediate the problem. Your data could have been leaked over the year-plus that the vulnerability could have been accessed. There is no way to know if it has been compromised.
Last week, the Heartbleed bug was identified as a weakness in the OpenSSL cryptographic library, potentially leaking two-thirds of the Internet's secure information from any websites utilizing this encryption style. While most major websites such as Google, Yahoo, and Facebook released patches quickly, it does little to actually remediate the problem. Your data could have been leaked over the year-plus that the vulnerability could have been accessed. There is no way to know if it has been compromised.
 On December 3, 2013, security company Trustwave discovered over two million stolen user passwords for popular online services like Facebook, LinkedIn, Google, Twitter, Yahoo, and 93,000 other websites. There's a high probability that you use one of the services affected by the hack. Is your personal information compromised?
On December 3, 2013, security company Trustwave discovered over two million stolen user passwords for popular online services like Facebook, LinkedIn, Google, Twitter, Yahoo, and 93,000 other websites. There's a high probability that you use one of the services affected by the hack. Is your personal information compromised?
 Last time, we spoke about password security, we went over the importance of using strong passwords to avoid identity theft. In part two, we will discuss three easy password solutions that can help you manage all of your different passwords.
Last time, we spoke about password security, we went over the importance of using strong passwords to avoid identity theft. In part two, we will discuss three easy password solutions that can help you manage all of your different passwords.
For sites you need to log into often, having your browser remember your password can save you time logging in, especially if you are using secure passwords that you might need to look up otherwise. There are circumstances where you might want to manage what personal information gets stored in your web browser.
The problem with carrying around an expensive, portable piece of equipment is that it's possible for someone to pick it up and run with it. According to LoJack, a security firm that focuses on stolen property, two million laptops are stolen each year. What should you do if you are a victim of laptop theft?
This has been a pretty common topic for us on the NetWorthy Systems blog. We've seen a lot of Beaumont clients and customers suffer the consequences when online retailers and other account providers experience a security breach. It is equally vital for consumers to know what to do in the event of a security breach as it is the company that is actually breached.
Your identity has quite a lot of value, especially in the wrong hands. Security firm ZoneAlarm put together some numbers in 2011 concerning identity fraud, and it even shocked us. Let's talk about a few of these statistics and what it means.
On the topic of identity theft, social media accounts are becoming a high target for hackers, especially for spreading malicious viruses. To some, losing control over their Facebook or Twitter accounts could be just as devastating as having their credit card stolen. Trouble is, for many users, having one login account stolen means hackers have access to their other accounts too.












