Have any question?
Call (409) 861-4450
Call (409) 861-4450
Microsoft Word has long since established itself as the primary word processing software in the business world, but even some power users don’t necessarily know about all of the hidden features that exist in it. Here are three of the best Word capabilities that you’ll be sure to use next time you’re in a pinch.
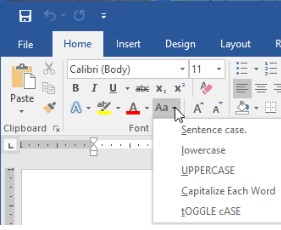
Changing the Case of Your Text
Sometimes you might be typing something and accidentally hit the Caps Lock key instead of Shift. Instead of deleting everything and retyping it, you can simply use a new Microsoft Word feature that lets you choose the case of your new text. You can select Sentence case, Lower-case, and Uppercase, as well as Capitalize Each Word and tOGGLE cASE.
Automatically Update the Date and Time
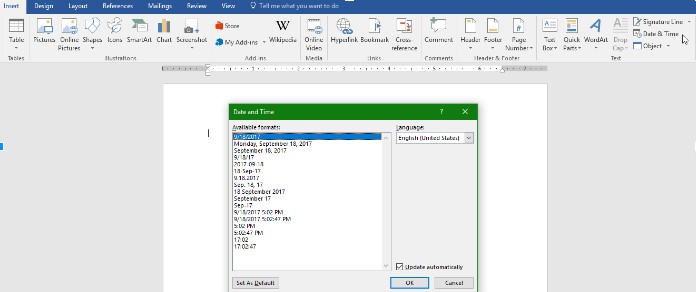
Most businesses will use digital correspondence, but there are times when you’ll have to use direct mail. Most organizations will send out a welcome letter to new clients via traditional postage, with some personalization to match the client. Word can be used to make sure that the information offered in the latter is updated automatically. You can set your templates to auto-update with the current date and time.
In the Insert tab, click on the Date & Time button. This will open up a pop-up window. Next, just click on the date format and select the Update Automatically box in the bottom-right corner. Your date will automatically be updated every time you open or try to print the document.
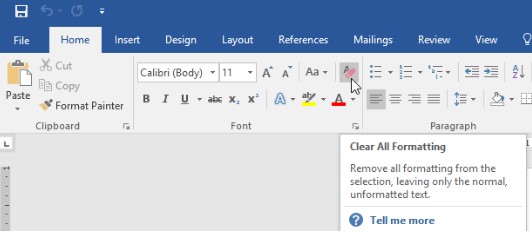
Eliminate Unwanted Formatting
When you copy and paste text from a source, it retains the formatting of the original document. If you’re not careful, this text could persist throughout the remainder of your document edits. Thankfully, there is a very simple fix to this issue. Microsoft Word has a keyboard command that you can use to eliminate formatting, and it’s Ctrl + Space. Better yet, you can just use the little eraser button in Word’s settings to eliminate formatting.
Want even more great tips and tricks? Visit our blog regularly for more technology-related tips.
Get the Knowledge You Need to Make IT Decisions
Technology is constantly evolving, and keeping up can feel overwhelming. Whether you want to understand cybersecurity threats, explore automation, or learn how regulations like PCI DSS impact your business, we’ve made it easy to access clear, straightforward insights on key IT topics.
Learn more about what NetWorthy Systems can do for your business.
NetWorthy Systems
701 W. Division Ave Suite 100
Orange, Texas 77630