Have any question?
Call (409) 861-4450
Call (409) 861-4450
 Wireless Internet access is a luxury that seems commonplace, but there are many who experience trouble with their connections on a daily basis. Sometimes the problem stems from familiar issues that could happen at any minute, but other times the issues might not be so obvious. Either way, you should be aware of the most common disruptions to your WiFi signal, even those that you might not consider problems.
Wireless Internet access is a luxury that seems commonplace, but there are many who experience trouble with their connections on a daily basis. Sometimes the problem stems from familiar issues that could happen at any minute, but other times the issues might not be so obvious. Either way, you should be aware of the most common disruptions to your WiFi signal, even those that you might not consider problems.
 Have you ever wondered how your PC is identified from the billions of devices out there in the world today? Just like every human being has specific physiological traits that make up who they are, your computer’s IP address is somewhat unique to your machine, and it can say a lot about you. Therefore, it’s important that you are able to identify your own IP address when you need to.
Have you ever wondered how your PC is identified from the billions of devices out there in the world today? Just like every human being has specific physiological traits that make up who they are, your computer’s IP address is somewhat unique to your machine, and it can say a lot about you. Therefore, it’s important that you are able to identify your own IP address when you need to.
 We all know how annoying WiFi can be at times. Sometimes it’s simply a bad connection, or perhaps there are too many devices accessing your network. Or, maybe it’s your sneaky neighbor stealing your WiFi. Regardless of what the cause is, there’s a way to check your WiFi usage in the Windows operating system.
We all know how annoying WiFi can be at times. Sometimes it’s simply a bad connection, or perhaps there are too many devices accessing your network. Or, maybe it’s your sneaky neighbor stealing your WiFi. Regardless of what the cause is, there’s a way to check your WiFi usage in the Windows operating system.
 When the Internet was first established, malware and hacking were in their infancy, and not as much of an immediate problem as they are today. Thanks to this fact, the Internet wasn’t really created with a certain security design in mind, and has instead adapted to shifts in its environment. Unfortunately, as hackers grow more powerful, several of these patchwork protocols are growing outdated.
When the Internet was first established, malware and hacking were in their infancy, and not as much of an immediate problem as they are today. Thanks to this fact, the Internet wasn’t really created with a certain security design in mind, and has instead adapted to shifts in its environment. Unfortunately, as hackers grow more powerful, several of these patchwork protocols are growing outdated.
 The Internet of Things is changing the face of web-connected devices as we know it. Some would argue that the world isn’t ready for the IoT, but it’s on its way nonetheless. But what really constitutes the Internet of Things? InfoWorld suggests that a lot of what the public sees as the Internet of Things shouldn’t be classified as IoT devices. Therefore, we need a more substantial definition for this revolutionary phenomenon.
The Internet of Things is changing the face of web-connected devices as we know it. Some would argue that the world isn’t ready for the IoT, but it’s on its way nonetheless. But what really constitutes the Internet of Things? InfoWorld suggests that a lot of what the public sees as the Internet of Things shouldn’t be classified as IoT devices. Therefore, we need a more substantial definition for this revolutionary phenomenon.
 Major retailers are having a rough time of it these days concerning the security of their customer's financial information. Last December, Target was hit with malware that compromised 40 million customer credit and debit card accounts, and recently, Home Depot was hit with the same malware. What's a connoisseur of mass-produced boxed goods to do?
Major retailers are having a rough time of it these days concerning the security of their customer's financial information. Last December, Target was hit with malware that compromised 40 million customer credit and debit card accounts, and recently, Home Depot was hit with the same malware. What's a connoisseur of mass-produced boxed goods to do?
 In Europe, there's a lot of discussion about whether or not citizens have the right to be forgotten, or rather, be forgotten by search engines. According to a May 2014 ruling, search engines must consider requests from the public for removal of content. Not just any content, though; according to ZDNet, the content must be "inadequate, irrelevant, or no longer relevant." As you might guess, this concept is extremely controversial.
In Europe, there's a lot of discussion about whether or not citizens have the right to be forgotten, or rather, be forgotten by search engines. According to a May 2014 ruling, search engines must consider requests from the public for removal of content. Not just any content, though; according to ZDNet, the content must be "inadequate, irrelevant, or no longer relevant." As you might guess, this concept is extremely controversial.
 Does your company have dedicated antivirus software to protect it against the annoying threats on the Internet? Sometimes, a computer virus can weasel its way past your software, but there's no greater frustration than when you realize that the reason you contracted a virus is because an employee disabled your software. Don't let this happen to you!
Does your company have dedicated antivirus software to protect it against the annoying threats on the Internet? Sometimes, a computer virus can weasel its way past your software, but there's no greater frustration than when you realize that the reason you contracted a virus is because an employee disabled your software. Don't let this happen to you!
 We all know about the cryptocurrency Bitcoin, but do you know about Dogecoin? Its figurehead, the grammatically-challenged Shiba Inu, quickly became an Internet sensation called the Doge meme, and was adopted as the mascot for Dogecoin. However, before you go out and buy yourself some Dogecoin for you and your buddies, you should know that its database, the Doge Vault, has been hacked.
We all know about the cryptocurrency Bitcoin, but do you know about Dogecoin? Its figurehead, the grammatically-challenged Shiba Inu, quickly became an Internet sensation called the Doge meme, and was adopted as the mascot for Dogecoin. However, before you go out and buy yourself some Dogecoin for you and your buddies, you should know that its database, the Doge Vault, has been hacked.
 Can you tell the difference between the two words, Internet and Intranet? The difference is much more than simply two letters. Both are valuable marketing tools, particularly for small businesses, but what exactly differentiates them from each other? The key to understanding this is a simple English lesson.
Can you tell the difference between the two words, Internet and Intranet? The difference is much more than simply two letters. Both are valuable marketing tools, particularly for small businesses, but what exactly differentiates them from each other? The key to understanding this is a simple English lesson.
 19 years ago, a class of fifth graders from Helena, Montana was featured in a PSA video that, looking back, made some eerily-close predictions about how the Internet is used today. When this PSA was shot in 1995, only 0.4% of the world's population regularly used the Internet. Today, nearly 39% of the world uses it, and for good reason, as predicted all those years ago.
19 years ago, a class of fifth graders from Helena, Montana was featured in a PSA video that, looking back, made some eerily-close predictions about how the Internet is used today. When this PSA was shot in 1995, only 0.4% of the world's population regularly used the Internet. Today, nearly 39% of the world uses it, and for good reason, as predicted all those years ago.
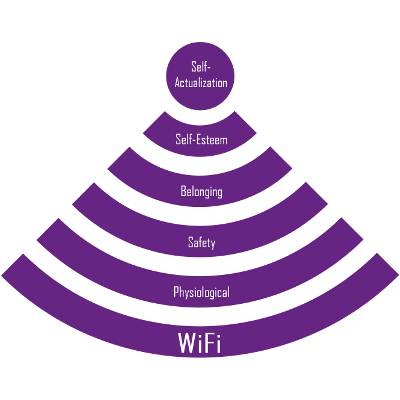 In 1943, psychologist Abraham Maslow published a paper about human motivation that would become the well-known Maslow's Hierarchy of Needs. His theory states that before self-actualization can be achieved, four needs must first be met, like esteem, belonging, safety, and physiological (the most basic which includes, air, food, water, etc.). In 2014, we feel the need to add one more layer to Maslow's pyramid: WiFi.
In 1943, psychologist Abraham Maslow published a paper about human motivation that would become the well-known Maslow's Hierarchy of Needs. His theory states that before self-actualization can be achieved, four needs must first be met, like esteem, belonging, safety, and physiological (the most basic which includes, air, food, water, etc.). In 2014, we feel the need to add one more layer to Maslow's pyramid: WiFi.
 Since the late 1990s, digital information, music, movies, software, and content has been at risk of being illegally shared worldwide for free. Peer-to-peer file sharing has forced entire industries to shift the way they do business as they try to counteract the illegal practice. The new Copyright Alert System will attempt to quell illegal file sharing.
Since the late 1990s, digital information, music, movies, software, and content has been at risk of being illegally shared worldwide for free. Peer-to-peer file sharing has forced entire industries to shift the way they do business as they try to counteract the illegal practice. The new Copyright Alert System will attempt to quell illegal file sharing.
Get the Knowledge You Need to Make IT Decisions
Technology is constantly evolving, and keeping up can feel overwhelming. Whether you want to understand cybersecurity threats, explore automation, or learn how regulations like PCI DSS impact your business, we’ve made it easy to access clear, straightforward insights on key IT topics.
Learn more about what NetWorthy Systems can do for your business.
NetWorthy Systems
701 W. Division Ave Suite 100
Orange, Texas 77630